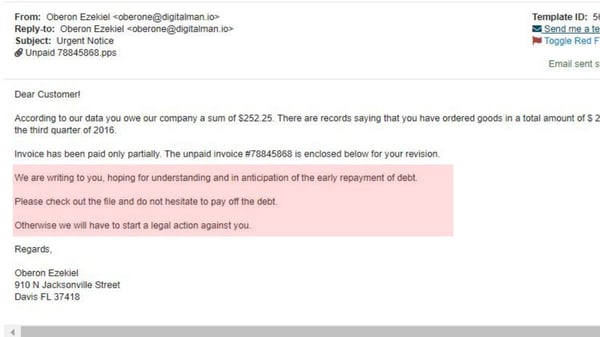
Have you ever opened an email that just didn’t seem right? Perhaps a client sent you an unexpected invoice, or Microsoft requested provided a link to unlock your account. Cyber criminals work day and night to try to spoof computer users. They have the technology available to alter emails in many ways to make them seem legitimate in order to get you to click or respond.
Your email filters have an average 10.5-15% failure rate, so you need to practice security awareness skills to keep your information safe. If your email filters are doing a good job, you can probably check your spam and recognize a handful of phishing emails that are easy to spot. Read more to see the warning signs of a social engineering attack.
We’ve compiled a list of red flags to look out for when phishing emails are smart enough to slip through spam filters to your inbox.
Ask yourself these questions when opening an email, and you’ll be able to recognize a phishing attempt.
Check the From: line
- Do you recognize the sender’s email address, and is it someone you usually communicate with?
- Is the email from someone outside your organization, and is it related to your job responsibilities?
- Is the email unusual or out of character?
- Is the sender’s email address from a suspicious domain? Check for any misspellings, or if the domain uses a general term, such as HR@yourdomain.org or IT@yourdomain.org.
- Is the email unexpected with a hyperlink or attachment from someone who you haven’t communicated with recently?
Check the To: Line
- Do you know the other people the email was sent to, and was it sent to an unusual mix of people?
- Are people included on the email that are outside your organization?
Check the Hyperlinks
- Did you hover over the hyperlink, and make sure it links to the correct website?
- Is there a long hyperlink in an email without any other information? Never click this link!
- Does the hyperlink have something misspelled, or made to look correct with a different letter in place? An example would be armazon.com
Check the Date and Time
- Was the email sent at an unusual time, such as 3 AM?
Check the Subject
- Is the subject line irrelevant, or does not match the message content?
- Is the email message asking you to reply to something you never sent or requested?
Check the Attachments
- Did the sender include an attachment that you weren’t expecting or that doesn’t make sense?
- Is there a potentially dangerous file type attached? The only file type safe to click on is a .txt file.
Check the Content
- Is the sender asking you to click on a link or open an attachment to avoid a negative consequence or gain something of value? An example would be, “click on the link or we will take legal action”.
- Is the email out of the ordinary or have bad grammar and spelling errors?
- Is the sender asking you to click on a link or open an attachment that seems odd or illogical? An example could be your HR department sending you a link to review your CEO and asking you to be secret.
- Do you have an uncomfortable feeling about the senders request to open an attachment or click on a link?
- Is the email asking you to look at a compromising or embarrassing picture of yourself or someone you know?
These are all questions you should ask yourself when opening up an email. Cyber criminals tend to target computer users by using tactics to trick you. If anything ever seems odd, pick up the phone and call the sender to verify.
I’ll end this post with a personal story. A couple weeks ago, a client I interact with often sent me an email asking me to view the invoice attached. I knew the client wouldn’t be sending me an invoice, so I emailed them back asking if they meant to send the invoice to me. They replied immediately, and told me it was valid and to open it. I then called the person, and the client told me her email was currently locked and she was aware the hacker was logged in and sending emails in real-time on her behalf. I was VERY glad I called!
As a final word, always think before you click! You never know who is lurking behind the email.
Do you have any phishing attack stories you’d like to share? Leave them in the comments so we can all learn from each other.









Leave a Reply